In today’s digital age, going above and beyond to safeguard personal online information is not just a nice perk to offer — it’s a necessity. All businesses, including child care centers, must take steps to protect their own personal data as well as their customers’ sensitive information, and it’s vital to use the best practices in child care security.
As a child care director or owner, you must help families keep their information safe on their end as well … something that is growing increasingly difficult as cybercrime becomes more prevalent.
The three primary ways in which cyber-attackers break into an organization are stolen credentials, phishing (when an attacker sends a genuine-looking email to deceive recipients into carrying out harmful instructions such as clicking on a link, opening an attachment, providing sensitive information or transferring money) and exploitation of vulnerabilities, according to the Verizon 2023 Data Breach Investigations Report.
Here are some more alarming statistics:
- One of the Verizon report’s findings is that 83% of breaches are initiated by “external attackers” looking for quick financial gain. Organized crime gangs and networks initiate eight out of every 10 breaches, 95% of the time for financial gain.
- The most common cause of a data breach is weak and stolen credentials. In fact, 80% of data breaches are caused by poor or reused passwords.
Let’s take a look at what child care centers and daycares must do to keep sensitive data safe and how Procare can help you do that.
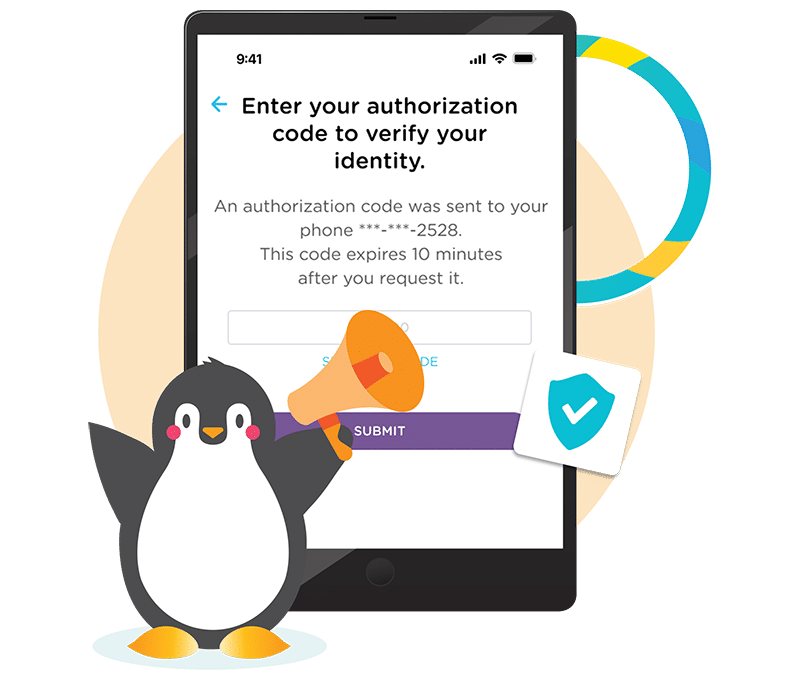
Two-Step Authentication
Rather than just asking for a username and password to log in, two-step authentication requires another verification factor to decrease the likelihood of a successful cyber attack.
Only 26% of companies use this form of authentication, yet Microsoft has found that this extra step blocks 99.9 percent of automated cyberattacks on its platforms, websites and other online services.
By using two-step authentication your families can create a robust defense against unauthorized access, data breaches and potential cyber attacks to help ensure that their personal information stays secure.
Two-step verification allows parents to add a phone number and/or email address to their Procare user login to receive verification codes whenever an attempt is made to log into their account.
A year-long study conducted by Google on two-step verification found that a text code sent to a recovery phone number helped block 100% of automated bots, 96% of bulk phishing attacks and 76% of targeted attacks.
So there’s solid proof that two-step authentication works, even though only a quarter of companies are using it.
Procare Solutions has implemented this additional layer of security to safeguard financial and other personal information. It’s optional for you and the families you serve but is highly recommended to ensure sensitive data is more strongly protected.
Think of this example: let’s say a mom’s smartphone is stolen. If two-step authentication is enabled on apps and other services, it prevents unauthorized access to photos of her children and to her financial information.
So even if thieves or hackers manage to steal or guess a password, they would still require the other factor(s) to gain access.
Uphold Customer Trust and Your Reputation
When customers provide their personal information, they trust that it will be handled responsibly and securely. A breach of this trust can severely damage your child care center’s reputation.
A Forbes Insight report found that 46% of organizations had suffered reputational damage as a result of a data breach and 19% of organizations suffered reputation and brand damage as a result of a third-party security breach.
By safeguarding their personal data, your child care business can demonstrate its commitment to respecting the privacy of your families and reinforcing the trust they have placed in you.
Recent news coverage has highlighted concerns about how well child care management software protects sensitive data. Procare Solutions is the leader in taking steps beyond just what is required by law to secure data. When your center uses Procare, you can assure your families that you are offering the best-in-class software as well as industry-leading security measures.
Let’s take a look at some of these protections.
How Procare Solutions Protects Data
Procare Solutions treats all data provided in-solution by customers as sensitive.
Access to sensitive information requires an authorized user to log in with a strong password. We require at least 12 characters and allow a wide variety in what those characters are for maximum complexity and strength.
Only people authorized to see your data can view it and your data is encrypted in transit over the internet and while at rest in our databases.
Our encryption, authentication and access controls satisfy industry standards as defined by bodies like the payment card industry.
Procare Solutions employees undergo background checks, security policy review and acknowledgment and repeated reinforcement security awareness training throughout the year to make sure they are up to date on proper security practices.
Our software meets or exceeds all data requirements required by law and is especially proud to be certified as SOC, type 2 complaint. In the cybersecurity world, this is a big deal. We also perform secure code testing prior to the release of production software.
There are two SOC ratings. A type 1 classification is given after an auditor determines system is designed suitably to achieve the related objectives on a specified date.
To earn an SOC 2 classification, an organization must meet all the requirements in type 1, but goes further to focus on testing the controls to prove their effectiveness over nine months.
Procare Solutions is the only child care management software to earn this coveted certification. We’ve been battle tested to give your center and your families peace of mind.
Know Who Is Authorized to Pick Up Children

With Procare, each person who is authorized to pick up a child is issued his or her own unique four-digit pin. That includes parents and other people who are allowed to take a child from your center.
This is beneficial during peak times when your center is bustling with many families arriving at the same time to pick up children. It’s often hard to keep track of everyone coming and going. Enabling a pin gives you confidence in knowing that you’re providing your families, as well as your staff, an extra layer of security regarding who is allowed in the building and authorized to pick up children.
And when you have changes in drop-off or pick-up procedures at your center, you can quickly alert parents with the Procare child care mobile app, which allows you to send messages either individually or via group messaging.
Once a child is checked in or out, that information is immediately populated into an attendance dashboard, where you can see how and when they checked in or out, their assigned room, hours attended, absences and parents’ signatures (if applicable).
You can also track ratios and compile daily, weekly, biweekly and monthly reports!
Enable Contactless Check-in
Relying on paper sheets to record when children are dropped off and picked up just doesn’t work anymore. It makes these times of day too chaotic and it doesn’t give you the information you need to adhere to staff-to-child ratios in real time.
It’s just not a way of doing business that inspires confidence.
Procare’s integrated technology allows families and your staff to use QR codes and/or GPS technology for a completely touch-free check-in and check-out system.
Parents can check in their children using the Procare child care mobile app without entering your building or by scanning a code once inside.
Each school and child care center uses a unique QR code that can be displayed on a tablet, computer, smartphone or printed on paper and displayed at your daycare.
When parents or other family members arrive, they simply pull up the Procare mobile app on their phone, select the QR code icon and scan. After scanning the code, the parent will be able to check in their child directly from their phone.
Procare’s technology allows your teachers and other staff to sign in and sign out easily and quickly using a tablet at your center or their own phone.
Timecards automatically are updated, which frees up your time spent on a mundane administrative task.
Procare Solutions is the only provider of child care management software that uses geofencing on contactless check-ins, which means that a person must much be within a certain distance from your center to check in a child. That means a “bad actor” in another country, for instance, could not check a child in or out over the internet.
Use Procare to Protect Your Data
As a child care center, you already hold the huge responsibility of providing a safe and nurturing environment for our children to thrive. By prioritizing robust security measures, you can be confident that you’re also taking the responsibility of protecting data seriously as well.
We empower over 37,000 child care centers around the country to simplify child care operations and create meaningful connections with families by providing technology, expertise and unparalleled service. Ensuring your trust remains the foundation of our mission.

Rest assured that we adhere to strict security measures and compliance protocols, upholding the utmost protection of your data. Read more about our security and compliance practices.